AceFL: Federated Learning Accelerating in 6G-enabled Mobile Edge Computing Networks – IEEE
Heterogeneity among distributed edge devices and the limitation of resources may degrade the training efficiency of Federated Edge Learning over 6G-enabled mobile edge computing (MEC) networks. Taking this challenge into account, a novel federated learning scheme is proposed in this paper to accelerate the training process.
Áika: A Distributed Edge System for AI Inference – MDPI
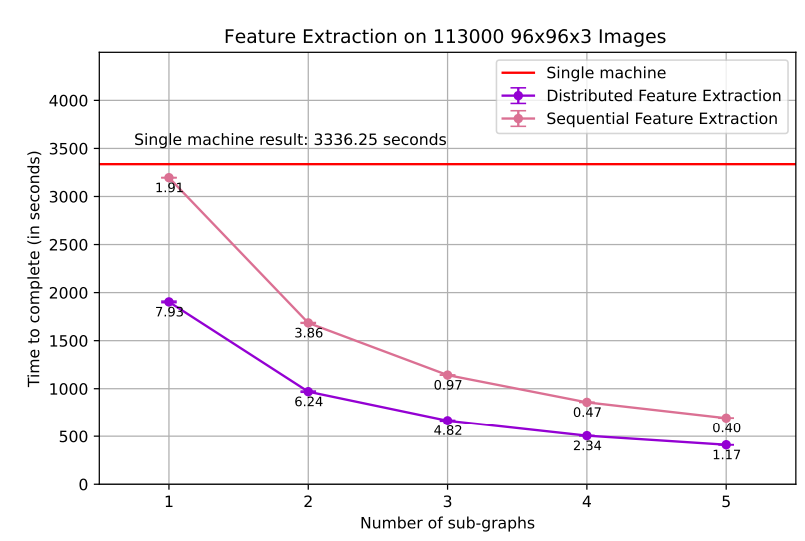
In this paper, we present Áika, a robust system for executing distributed
Artificial Intelligence (AI) applications on the edge. Áika provides engineers and researchers with
several building blocks in the form of Agents, which enable the expression of computation pipelines
and distributed applications with robustness and privacy guarantees.
ETSI – MEC Security White Paper: Status of Standards Support & Future Evolutions

This White Paper, the very first initiative in this domain, aims to identify aspects of security where the nature of edge computing leaves typical industry approaches to cloud security insufficient.
Edge computing environments are characterized by a complex multi-vendor, multi-supplier, multi-stakeholder ecosystem of equipment and both HW and SW devices. Given this overall level of system heterogeneity, security, trust and privacy are key topics for the edge environments.
In this heterogeneous scenario, end-to-end MEC security considers the impact on the elements coming from all stakeholders involved in the system. The paper provides an overview of ETSI MEC standards and current support for security, also complemented by a description of other relevant standards in the domain (e.g. ETSI TC CYBER, ETSI ISG NFV, 3GPP SA3) and cybersecurity regulation potentially applicable to edge computing. The White Paper concludes on a general perspective of future evolutions and standard directions on MEC security.
Colt: The Evolving Path to Cloud Adoption
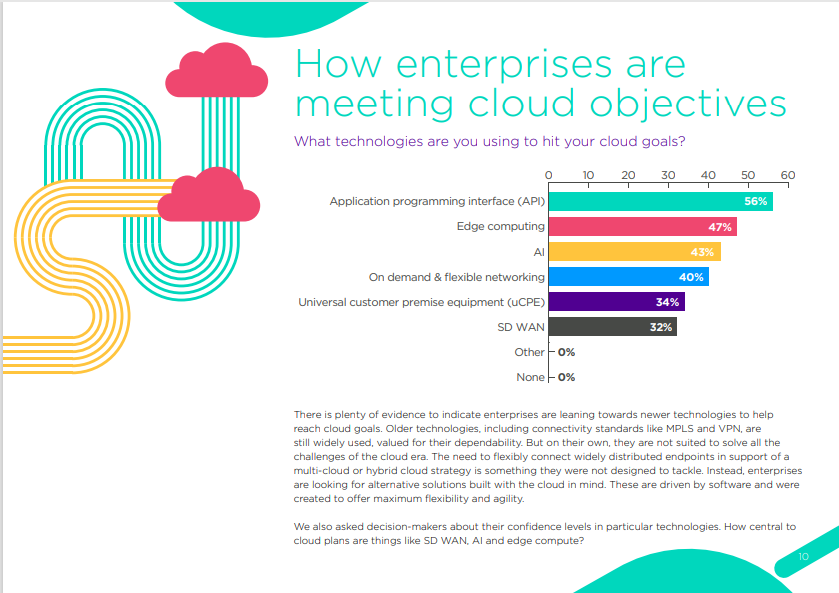
Colt Telecoms has released a report compiled by Censuswide, exploring what is driving the next era of cloud adoption.
It surveyed 400 IT decision-makers and C-level executives, across Europe and Asia.
• There is an increase in cloud projects, driven by technology evolution and emerging solutions.
• Businesses have a hunger to transform digitally, reduce legacy standards and embrace a whole new generation of compute, connectivity and partnerships.
• APIs and edge computing were some of the most significant elements according to respondents.
Recent Advances in Edge Computing for 6G – IEEE
Edge computing is a new technology that enables 6G development by bringing cloud capabilities closer to end users to overcome traditional cloud flaws