As we edge closer to the dawn of the 6G era, the excitement about its transformative potential is tempered by concerns over security. The leap forward in speed, capacity, and connectivity will undeniably bring significant benefits, but it also introduces complex security challenges that demand innovative solutions.
In this blog, we’ll discuss the potential threats data technologists anticipate with a 6G roll out, as well as safeguards we can start to put in place to protect ourselves against these challenges. Let’s take a closer look at the security landscape of 6G technology.
The evolving threat landscape with 6G technology
Launching 6G has the potential to exponentially increase the volume of data transmitted over networks, thereby expanding the attack surface for potential cyber threats. With 6G’s integration of Artificial Intelligence (AI), Internet of Things (IoT) devices, and more sophisticated network infrastructures, securing these vast, interconnected systems against breaches and cyber-attacks becomes a monumental task.
The key challenge lies in safeguarding against both known threats and those we haven’t even anticipated yet. Tricky, we know. There are efforts underway to anticipate ongoing threats and concerns with 6G, but we still have a ways to go.
What are the security concerns with 6G?
When considering what threats and vulnerabilities people should start to look out for as we think about a 6G launch, there are several. These are the key concerns we’re seeing most in the field:
1. Data privacy and integrity
As 6G networks facilitate faster data exchanges, ensuring the privacy and integrity of this information becomes a paramount concern. The risk of intercepting and manipulating data by unauthorized entities poses a significant threat to user privacy and data security. Universities have been testing scenarios in which eavesdroppers, for example, could get access to data transmission in the Terahertz band.
2. Network vulnerabilities
The complexity of 6G networks, with their dense web of connected devices and reliance on AI, introduces new vulnerabilities. These include potential backdoors for attackers, risks of AI exploitation, and the challenges of securing vast IoT ecosystems. Researchers are also concerned about adversarial attacks using AI.
3. Advanced persistent threats (APTs)
6G networks will likely face sophisticated cyber-attacks by well-resourced and persistent adversaries. These APTs are capable of executing multi-vector attacks to infiltrate networks, often remaining undetected for extended periods.
4. Identity theft and fraud
The increase in data throughput and connectivity in 6G networks could lead to more sophisticated identity theft and fraud schemes. Protecting against such threats will require robust identity verification and authentication measures.

How can we make 6G more secure?
Addressing 6G security challenges will require a collaborative effort. By fostering partnerships between governments, industry stakeholders, and cybersecurity experts, it’s possible to establish global standards and regulations that ensure comprehensive security measures are in place. Such collaboration will be key in developing a secure, reliable foundation for the 6G future. After all, it’s our collective responsibility to prioritize security with any new technology.
To counter these risks and challenges, there are four key safeguards we can start putting in place as soon as today, including:
1. Encryption and anonymization
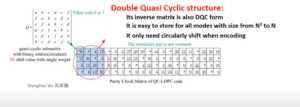
Cutting-edge encryption methods will be vital when 6G rolls out. Quantum encryption, for instance, offers a promising solution with its potential to create virtually unbreakable encryption, ensuring the confidentiality and integrity of data transmitted over 6G networks. This advanced approach could be pivotal in protecting against sophisticated cyber-attacks.
Zero trust is another method to secure networks – that is, no person or device should be trusted by default, regardless of being from inside or outside the network.
2. AI and machine learning for security
AI will play a crucial role in enhancing 6G security. By employing AI-driven algorithms for real-time threat detection and response, 6G networks can achieve a level of proactive security management previously unattainable. These systems can continuously learn and adapt to new threats, ensuring the network’s resilience against evolving cyber-attacks.
>> Head on over to our guide if you want to learn more about 6G and AI
3. Comprehensive security frameworks
Developing and implementing comprehensive security frameworks that address the unique vulnerabilities of 6G technology. This includes regular security assessments and updates to adapt to evolving threats.
4. User awareness and education
Enhancing user awareness and education is a critical defense mechanism against cyber threats in the 6G era. This involves comprehensive training programs and initiatives aimed at informing users about the nature of cyber threats such as phishing, social engineering, and the methods hackers use to gain unauthorized access. It’s about cultivating a culture of cybersecurity mindfulness, where users are equipped with the knowledge to identify potential threats and empowered with best practices for safeguarding their data and devices.
For more information on this topic, download the “Conceptualizing Security in a 6G World” whitepaper.
Preparing for a safer 6G rollout
The transition to 6G offers a window into a future filled with incredible potential, provided we navigate its security challenges with foresight and innovation. By investing in advanced encryption technologies, leveraging AI in cybersecurity, and fostering global collaboration, we can secure the 6G era against the threats it faces, ensuring a safe, interconnected world for everyone.
For more insights into the rapidly evolving world of 6G technology and its security landscape, subscribe to our newsletter for the latest updates delivered right to your inbox.